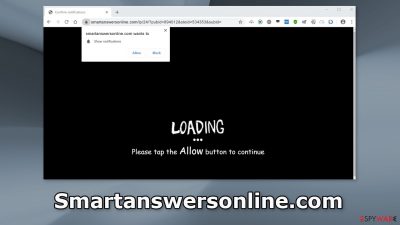
Smartanswersonline.com may seem innocent at first glance, but lurking beneath its façade lies an annoying and potentially hazardous threat. Clicking the “Allow” button on this deceptive website can unleash a barrage of pop-up spam, even when your browser is closed. This dubious tactic is designed to generate revenue through pay-per-click advertising, a scheme often exploited by cybercriminals.
The dangers associated with Smartanswersonline.com extend beyond mere annoyance. These pop-up ads can lead unsuspecting users to perilous websites, where personal information may be compromised, and devices may become infected with malware or potentially unwanted programs (PUPs).
The content of these intrusive ads ranges from adult materials to fake antivirus deals, software offers, surveys, and giveaways, among others. It is crucial to disable these pop-ups promptly, especially if multiple users share the affected device. In this article, we provide a comprehensive guide on how to eliminate these pop-ups and safeguard against future spam.
Understanding Smartanswersonline.com
Name: Smartanswersonline.com
Type: Push notification spam; adware
Symptoms: Pop-up ads appear after clicking “Allow”
Distribution: Shady websites, deceptive ads, redirects, freeware installations
Dangers: Links in push notifications can lead to dangerous websites, risking personal information and monetary loss
Elimination: Block push notifications via browser settings
Additional Steps: Consider using a repair tool like ReimageIntego after removal to address any residual damage
The Spread of Smartanswersonline.com
Smartanswersonline.com typically doesn’t appear in search results. Instead, it lurks on unregulated, shady websites. Illegal streaming sites, known for their deceptive ads and redirects, are common culprits hosting such dubious content. They often employ fake “Download” and “Play” buttons that open new tabs, even though efforts have been made to eradicate these practices.
To protect yourself, stick to websites you know and trust. Avoid clicking on random links and ads, even if they seem to endorse legitimate products and services. Opt for legitimate and secure streaming platforms that offer a small monthly subscription fee for unlimited content access.
Blocking Smartanswersonline.com Notifications
Push notifications are subscription-based, allowing users to enable or disable them manually. Follow these steps to block Smartanswersonline.com notifications in popular web browsers:
Google Chrome (desktop):
- Open Google Chrome and go to Menu > Settings.
- Scroll down and click on Advanced.
- In the Privacy and security section, select Site Settings > Notifications.
- Look for a suspicious URL under the Allow section.
- Click the three vertical dots next to it and choose Block.
Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to Sites section.
- Find the unwanted URL and toggle the button to the “Off” setting.
Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security.
- Under Permissions, locate Notifications and click the Settings button next to it.
- In the Notification Permissions window, find the URL in question.
- Select Block and click Save Changes.
Safari:
- Click on Safari > Preferences.
- Go to the Websites tab and, under General, select Notifications.
- Find the web address you want to block, click the drop-down menu, and select Deny.
Microsoft Edge:
- Open Microsoft Edge, click the Settings and more button (three horizontal dots) at the top-right.
- Select Settings, go to Advanced, and under Website permissions, choose Manage permissions.
- Find the URL in question and toggle the switch to turn off notifications.
Microsoft Edge (Chromium):
- Open Microsoft Edge, go to Settings, and select Site permissions.
- Choose Notifications on the right, and under Allow, find the unwanted entry.
- Click More actions and select Block.
Clearing Cookies and Cache
After encountering Smartanswersonline.com, it’s advisable to clear your browser’s cookies and cache. Websites often use these tracking technologies to collect data, including your IP address, geolocation, visited websites, clicked links, and online purchases. While cookies and cache are essential for personalized user experiences, they can also be exploited for revenue generation by selling data to advertising networks and third parties. Consider using a reliable tool like ReimageIntego to stop tracking, delete collected information, and fix system errors.
Checking for Adware Infections
Unwanted browser behavior, such as Smartanswersonline.com pop-ups, may result from potentially unwanted programs (PUPs). These programs can generate commercial content without users’ consent and are often disguised as helpful tools to evade detection.
To check for and remove adware, follow these steps:
Windows 10/8:
- Enter “Control Panel” in the Windows search bar and hit Enter.
- Under Programs, select “Uninstall a program.”
- Find the suspicious program in the list, right-click it, and choose “Uninstall.”
Windows 7/XP:
- Click on Windows Start > Control Panel.
- Under Programs, select “Uninstall a program.”
- Locate the unwanted application, click it, and select “Uninstall.”
Mac:
- From the menu bar, go to Go > Applications.
- Locate all related entries, click the app, and drag it to Trash.
To fully remove an unwanted app on Mac, access Application Support, LaunchAgents, and LaunchDaemons folders, and delete relevant files.
Preventative measures include using professional security tools like SpyHunter 5, Combo Cleaner, or Malwarebytes, which can scan for suspicious processes and provide warnings about potentially harmful files attempting to enter your system. Alternatively, follow our manual removal instructions for both Windows and Mac devices.
In today’s digital landscape, safeguarding your online privacy and security is paramount. While web browsers offer some protection, consider bolstering your defenses with a reputable VPN service like Private Internet Access. VPNs encrypt all incoming and outgoing traffic, ensuring your online activities remain private and secure.
Smartanswersonline.com and similar threats may attempt to invade your digital space, but with the right tools and precautions, you can fortify your defenses and maintain a safe online environment for yourself and your devices.